How do you carry out an effective risk assessment?
7 3.34000 out of 3.34000 points How do you start a risk assessment? Selected Answer: by clearly defining what you will assess Answers: by identifying countermeasures by generally defining controls by clearly defining what you will assess by mitigating risks
What are the steps in human health risk assessment?
Recommendations B. Current status of accepted recommendations C. Unapproved recommendations D. Timeline of the previous risk assessment 1 points QUESTION 10 1. Regarding risk assessments, _____________ define(s) what a system does. A. the mission of the system B. asset valuation C. operational characteristics D. an inventory
How do I assign a risk rating to my hazards?
May 15, 2019 · Question 18 0 out of 2 points How do you start a risk assessment? Answer s: by identifying countermeasures by generally defining controls by clearly defining what you will assess by mitigating risks
Who should carry out a new risk assessment?
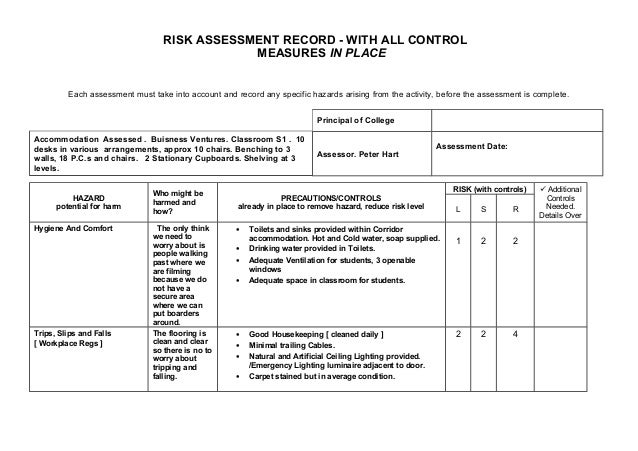
Sep 06, 2019 · A systematic approach to risk assessment Using a risk assessment tool or template ensures you take a systematic and thorough approach to assessing and controlling risks. Let's look at one example of a risk assessment template and the type of information they contain. Click on each number to learn more about each section.
What is risk assessment?
Risk assessment is one of the major components of a risk analysis. Risk analysis is a process with multiple steps that intends to identify and analyze all of the potential risks and issues that are detrimental to the business. This is an ongoing process that gets updated when necessary. These concepts are interconnected and can be used individually.
Why is it important to conduct a risk assessment?
Importance of Conducting Risk Assessments. Identifying hazards by using the risk assessment process is a key element when ensuring the health and safety of your employees and customers. OSHA requires businesses to conduct risk assessments.
What is risk communication?
Risk communication is the process of exchanging information and opinion on risk to concerned parties. Risk management is the proactive control and evaluation of threats and risks to prevent accidents, uncertainties and errors. Together with risk assessment, these are all vital elements that help make informed decisions such as mitigating risks.
What is iAuditor inspection?
iAuditor gives you the flexibility to power any inspection you require – onsite, underground, and across the globe. Inspect construction sites, restaurants inspections for food safety, conduct temperature checks, pre-flight checks, toolbox talks and more. It is the mobile forms inspection solution for all industries.
Is risk assessment required in the UK?
While in the UK, conducting risk assessments are a legal requirement as stated in the Health and Safety at Work Act. The specific regulation under this law can be retrieved from the Management of Health and Safety at Work Regulations Section.
What is a risk assessor?
The risk assessor (s) examine whether a stressor has the potential to cause harm to humans and/or ecological systems, and if so, under what circumstances. The risk assessor (s) gather information to determine the numerical relationship between exposure and effects.
What is human health risk assessment?
A human health risk assessment human health risk The likelihood that a given exposure or series of exposures may have damaged or will damage the health of individuals. is the process to estimate the nature and probability of adverse health effects in humans who may be exposed to chemicals in contaminated environmental ...
How does EPA assess human health?
A human health risk assessment includes four steps, which begin with planning: EPA begins a human health risk assessment by planning the overall approach with dialogue between the risk manager (s), risk assessor (s), and other interested parties or stakeholders. Members of the team: decide on team member roles.
When was Executive Order 13045 issued?
In light of what is now known about the greater susceptibility early in life to some stressors, Executive Order 13045 -- Protection of Children from Environmental Health Risks and Safety Risks -- was issued in 1997.
Why are children more vulnerable to environmental hazards?
In addition, children may be more vulnerable to environmental hazards because their systems are still developing, which often makes them less able to metabolize, detoxify, and excrete toxins.
Is mercury a toxic substance?
For pollutants that act as developmental toxicants, the same dose that may pose little or no risk to an adult can cause drastic effects in a developing fetus or a child. Methyl mercury is but one example of a chemical that is much more toxic early in life.
What is the objective of risk assessment?
The objective of a risk assessment is to understand the existing system and environment, and identify risks through analysis of the information/data collected. By default, all relevant information should be considered, irrespective of storage format. Several types of information that are often collected include:
Why is risk assessment important?
Communication —By acquiring information from multiple parts of an organization, an enterprise security risk assessment boosts communication and expedites decision making.
What is enterprise risk management?
Enterprise risk management (ERM) 1 is a fundamental approach for the management of an organization. Based on the landmark work of the Committee of Sponsoring Organizations of the Treadway Commission (COSO) 2 in the 1990s, its seminal Enterprise Risk Management— Integrated Framework, 3 has become a primary tool for organizational risk management. Regulators in the US have recognized the value of an enterprise risk approach, and see it as a requirement for the well-controlled organization. Two primary examples of this are compliance with the US Sarbanes-Oxley Act 4 and the US Health Insurance Portability and Accountability Act (HIPAA), 5 both of which require a periodic risk assessment.
How often should security risk assessments be conducted?
Security risk assessment should be a continuous activity. A comprehensive enterprise security risk assessment should be conducted at least once every two years to explore the risks associated with the organization’s information systems.
Why is information security important?
An information security framework is important because it provides a road map for the implementation, evaluation and improvement of information security practices. As an organization implements its framework, it will be able to articulate goals and drive ownership of them, evaluate the security of information over time, and determine the need for additional measures.
What is enterprise security risk assessment?
An enterprise security risk assessment can only give a snapshot of the risks of the information systems at a particular point in time. For mission-critical information systems, it is highly recommended to conduct a security risk assessment more frequently, if not continuously.
What are physical assets?
Physical assets, such as hardware, including those in the data center, network, and communication components and peripherals (e. g., desktop, laptop, PDAs) Operating systems, such as PC and server operating systems, and network management systems. Data repositories, such as database management systems and files.
What is START in medical?
The Short-Term Assessment of Risk and Treatability (START) is a concise clinical guide for the dynamic assessment of short-term (i.e., weeks to months) risk for violence (to self and others) and treatability. START guides the assessor toward an integrated, balanced opinion to evaluate the client’s risk across seven domains: violence to others, suicide, self-harm, self-neglect, unauthorized absence, substance use, and risk of being victimized. This structured professional guide is intended to inform clinical interventions and index therapeutic improvements or relapses.
What is START in psychiatry?
START is anticipated to be an effective means of reducing the cycling of mentally disordered persons through the civil psychiatric and criminal justice systems. It was developed for use with adults with mental, personality, and substance-related disorders, with relevance to correctional, civil, and forensic clients in the community ...
How to conduct a risk assessment?
To conduct your own risk assessment, begin by defining a scope of work. Maybe you want to improve health and safety measures in the shipping warehouse. Or, perhaps you want to identify areas of risk in the finance department to better combat employee theft and fraud. Whatever your objective, define it clearly.
What is risk assessment?
What is a Risk Assessment? A risk assessment identifies and evaluates the threats and risks of a specified situation. If you’re aware of a potential hazard, it’s easier to either reduce the harm it causes or (ideally) prevent it completely than to deal with the consequences.
What are the hazards of warehouses?
In a warehouse, for example, workers are at risk of many hazards such as: 1 Severe or fatal injury from falling 2 Repetitive strain injuries from manual handling 3 Sprains and fractures from slips and trips 4 Being crushed by falling objects 5 Being hit by (or falling out of) lift trucks 6 Crush injuries or cuts from large machinery 7 Moving parts of a conveyor belt resulting in injury 8 Exposure to hazardous substances
Why is risk assessment important?
Anticipating fraud and theft is a crucial component of a company’s antifraud efforts. Developing a risk assessment helps you identify hazards proactively so you can take precautionary measures or, if required, a risk response plan.
What is extreme risk?
They’re a high priority. An unlikely hazard with catastrophic consequences, such as an aircraft crash, is an extreme risk.
How to reduce the consequences of a disaster?
To reduce the consequences of risk, develop a mitigation plan to minimize the potential for harm. The third option is to avoid the risk. For catastrophic disasters, preventing the risk from occurring at all is the best (and often only) course of action.
What is the risk matrix?
Every risk assessment matrix has two axes: one that measures the consequence impact and the other measures likelihood. To use a risk matrix, extract the data from the risk assessment form and plug it into the matrix accordingly. Green is low risk. Yellow is medium risk. Orange is high risk.
Popular Posts:
- 1. which institute is best for medical transcription course in bangalore
- 2. what is financial management course
- 3. what is the best lsat prep course to take
- 4. how to write a college course curriculum
- 5. how long is billing and coding course
- 6. how long is medical assistant course
- 7. what is pmp training course
- 8. what is a course management system
- 9. what is business management course
- 10. how long is hvac course